On September 6, 2022, iThemes published a security advisory for the BackupBuddy plugin. As a global network, we can observe attacks in the wild as they hit our edge. This post shares what we’re seeing.
The BackupBuddy Plugin Vulnerability
iThemes’ post doesn’t disclose deep technical details, but summarizes the issue as:
This vulnerability could allow an attacker to view the contents of any file on your server that can be read by your WordPress installation. This could include the WordPresswp-config.phpfile and, depending on your server setup, sensitive files like/etc/passwd.
Practically speaking, that maps to a Local File Inclusion (LFI) class. LFI can expose (and in some cases execute) files on the same server. If an attacker can read
/etc/passwd or wp-config.php, they may also enumerate other sensitive artifacts (.env files, API keys, service credentials)—similar to what we discussed in our
AWS credential harvesting write-up.
Affected versions: BackupBuddy 8.5.8.0 through 8.7.4.1.
Monitoring Attacks & IOCs
iThemes suggests looking for local-destination-id, /etc/passwd, and wp-config. Be careful relying only on
/etc/passwd—it’s a very common target across many LFI probes. Here’s a clearer indicator pattern we’re seeing:
perezbox.com cdn-edge-canada-montreal1 198.27.68.131 200 783 - waf:js_challenge 08/Sep/2022:23:29:09 +0000
"GET /wp-admin/admin-ajax.php?local-download=wp-config.php&local-destination-id=0 HTTP/1.1"
"-" "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/84.0.4147.125 Safari/537.36"The interesting bits of the payload are:
admin-ajax.php?local-download=wp-config.php&local-destination-id=0
We’ve also observed the same structure via admin-post.php. Reviewing our telemetry, attacks began around August 27 and ramped after disclosure.
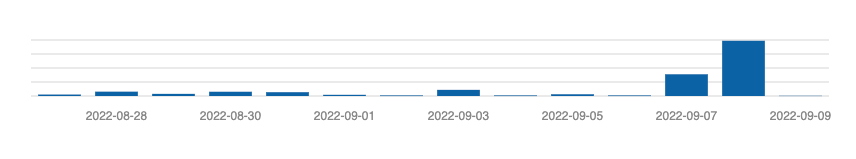
Peak yesterday hit ~4k attempts across multiple sites. Spikes following public advisories are expected and underscore the importance of fast patching. When speed isn’t possible, consider
protecting at the edge with a Web Application Firewall (WAF).
Using our Trunc logging platform, a quick query surfaced the top offending IPs (excerpt):
search "local-destination-id" | tail -n 2000 | cut -d " " -f 2 | sort -u -r
268, 195.178.120.89
58, 46.253.243.143
45, 20.229.10.195
43, 195.201.195.185
25, 176.31.226.16
24, 51.254.101.7
23, 51.210.134.180
22, 51.161.197.85
20, 103.57.222.214
19, 62.171.137.109
…WordPress Security & Supply Chain Risk
Like any ecosystem, WordPress has a supply chain—plugins, themes, and third-party services. The platform’s extensibility is its strength and a major risk amplifier.
As broader software-supply-chain conversations continue in InfoSec, we should expect—and prepare for—them within CMS communities.
To their credit, BackupBuddy removed licensing barriers for the security update:
We have made this security update available to all vulnerable BackupBuddy versions (8.5.8 – 8.7.4.1), regardless of your current BackupBuddy licensing status, so no one continues to run a vulnerable version of the BackupBuddy plugin.
Still, some organizations won’t update promptly; some admins won’t see the advisory; compromises will occur. Defense-in-depth matters.
All NOC customers were automatically protected from this vulnerability during the zero-day window via edge rules in our WAF.
NOC — Authoritative DNS, CDN & WAF
Accelerate and protect your sites with global DNS, edge caching, and an always-on web application firewall.
See Plans